7 steps to hack into someone’s bank account
- Sbi Account Transfer Form
- Online Account Opening In Sbi
- Sbi Account Statement
- Sbi Bank Account Hacking Software Price
Hacking Bank Accounts free download - ID Vault, Hacker 2005 - The Broken Link, Download Bank Account Data, and many more programs. This video helps the viewer to understand the basics of encryption and RSA encryption. Also this video explains the reasons for utilizing the hardness of pri. Hacking means getting an entry into the bank accounts and steal the money from the accounts. All accounts are sealed. The bank requires the authentication or authorisation from the accountholders in order to effect any withdrawal transactions C. 'Consent (as per annexure-I) for Data Sharing and use of personal information for opening of Savings / Current / Deposit Account with State Bank of India' Click here to.
7 Steps to hack a bank account
The experiment:
Herbert Thompson* in 2008 wanted to show the public how easy it was to access someone’s personal information and bank account.
He did the experiment on someone who he barely knew, a girl named Kim. Using the knowledge he knew about her, her name, where she was from, where she worked and roughly her age, he was able to access her bank account in ONLY 7 STEPS!!!
Read below to see how he did it – in the days before Facebook!
Step 1
Google search. He googles her. Finds a blog and a resume. (Thompson called her blog a “goldmine.”) He gets information about grandparents, pets, and hometown. Most importantly he gets her college email address and current Gmail address.
Step 2
Next stop: Password recovery feature on her bank’s web site. He attempts to reset her bank password. The bank sends a reset link to her email, which he does not have access to. He needs to get access to her Gmail.
Step 3
Gmail access. He attempts to reset her Gmail password but Gmail sends this to her college email address. Gmail tells you this address’ domain (at least it did in 2008 when Thompson conducted the experiments) so he knew he had to get access to that specific address.
Step 4
College email account page. Thompson clicks the “forgot password” link on this page and winds up facing a few questions. Home address, home zip code and home country? No problem, Thompson has it all from the same resume. The same resume found from the simple Google search done earlier. Then came a stumbling block: the college wanted her birthday. But he only had a rough idea of her age, no actual birth date.
Step 5
State traffic court web site. Apparently, you can search for violations and court appearances by name! And such records include a birth date. (Facebook also makes this piece of data very easy to get even if people do not note their birth year… Remember Thompson knew roughly how old Kim was.) But he had no luck with the Department of Motor Vehicles.

Step 6
Thompson goes back to the blog and does a search for “birthday.” He gets a date but no year.
Step 7
Finally, Thompson attempts the college reset password again. He fills in her birth date, and simply guesses the year. He gets it wrong. But the site gives him five chances, and tells him which field has the error. So he continues to guess. He gets access in under five guesses. He changes her college password. This gives him access to her Gmail password reset email. Google requires some personal information which he is able to get easily from her blog (e.g., father’s middle name.) Thompson changes the Gmail password and that gives him access to the bank account reset password email. Here again he is asked for personal information, but nothing that he could not glean from Kim’s blog (e.g., pet name and phone number.) He resets the bank password and bingo, has immediate access to all her records and money.
About avemcomp
How do Hackers Hack Bank Accounts and Personal Information? Most people studying hacking have a keen interest in learning how to can hack bank accounts. They become discouraged with the prevailing perception that it is almost impossible to hack credit cards, debit cards, or net banking passwords, which is true to an extent. Today I will discuss with you why hacking bank account information is tough and considered to be almost impossible. We will also discuss the different, contemporary methods that hackers use to hack bank accounts.
Online Account Opening In Sbi
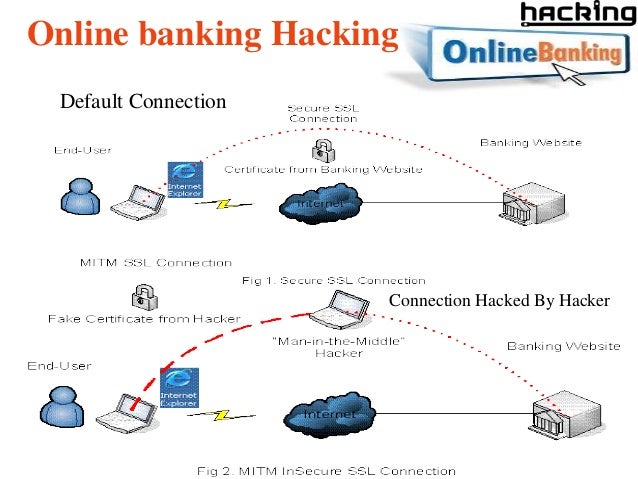
Almost everybody uses the internet nowadays to pay bills, book reservations and tickets, purchase items, or simply to transfer money. All of these online transactions involve money, meaning they’re using banking information, credit or debit card payments, or simply net banking. Most banks use SSL (Secured Sockets Layer) connection and at least 128 or 256 bit encryption for online banking and transaction purposes. An additional layer of security that companies are introducing is called “transaction PIN layer” which means that for each and every online transaction you have to enter your password, and that during transactions you have to enter a PIN, a type of password between 4 and 8 characters in length. Thus, banks do a lot of work to protect your credentials from the eyes of the world that may wish to gain access to your vital information.
Below, examples will illustrate to you how powerful the encryption method is:
- 40 bit encryption means there are 2^40 possible keys that could fit into the lock that holds your account information. That means there are billions of possible keys and using brute force is not an option. The only thing left now is a dictionary and rainbow attack. But it’s not only the security measure that banks use to secure information.
- 128 bit encryption means there are 2^88 times as many key combinations that are possible for 40 bit encryption. That means a computer would require exponentially more processing power and time than a 40-bit encryption to find the correct key.
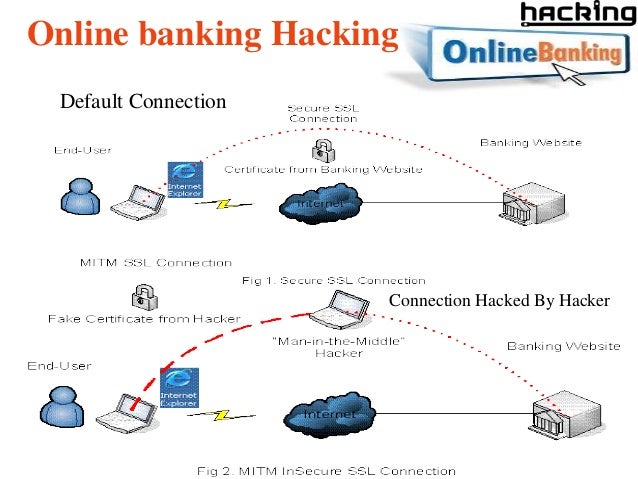
That’s a very powerful method of encrypting data sent from your machine to bank machine. But it’s all useless once your system has been compromised or hacked.
Now we’re going to discuss how all these security encryption can be bypassed and your system can be compromised online. There are several methods for exploiting such account information. Note: This is for educational purposes only (for more details read the disclosure).
Some of them are:
1. Phishing: We have discussed phishing on this website in a lot of tutorials, such as how to hack Gmail or Facebook accounts. But for newcomers, I’ll explain phishing in some detail. Phishing is a technique used to hack password and login details of a website. Phish pages are simply fake pages that look the original webpage where you’re taking the information from. The only difference between a phish page and the original page is the address bar link (for a normal user), redirection post, and get method (inside source for advanced users). How do you identify a fake link? Just check the address bar URL for a fake page or Phish page. It will be showing a different URL than the original. You can install a web security tool bar in your browser (like AVG and Crawler web security tool bars) to detect the phishing automatically, and to stop your browser from visiting Phishing pages.
Sbi Account Statement
Learn more about Phishing and how to protect yourself from Phishing:
2. Trojans:Trojans are a type of virus that steals your information. It can come in many forms like keyloggers or RATs (remote administration tools). A keylogger monitors all the keys that you have pressed on your physical keyboard, stores them in a log, and sends the details to hackers. RATs are an advanced form of keylogger that remotely monitors all your activities, whereas a keylogger is simply a functionality. Using RAT, a hacker can connect to your system anonymously, without your information when you are online. RATs have a huge list of functionalities and they are the best type of hacking tools available on the market. Now, how do you protect yourself from a keylogger? Just keep your antivirus software updated and install a keyscrambler that encrypts your keystrokes. Unfortunately, once the RAT enters your system you cannot do anything other than formatting your system. An RATs attack can only can be prevented before it enters in your system. For RAT prevention, please do not download any software or keygens online. Also avoid downloading freewares from new websites, only use certified websites like CNET, filehippo, etc. Avoid testing fake hack tools because most hacking tools have keylogger and RATs attached to them. Test it under secured conditions like on Virtual Users.
3. Session Hijacking: Most of us use wireless networks to access the internet and data flow in the form of packets and channels. We know that wireless networks are easier to hack due to their weak encryption. When hackers hack wireless networks, they take control of the internet data transfer and redirect the user to their intended path. Suppose you visit Gmail or Facebook, a hacker gains access and then he redirects you to somewhere on the page and captures your account details. Packet sniffing is another way to hack account information and credentials using the wireless networks. Hackers capture packets and decrypt information to get data in the form of plain text. Now how do you prevent this? The solution is also relatively simple, you just need to hide your SSID and BSSID from being discovered by the other networks. Leave the SSID or BSSID empty. Now hackers will not be able to discover your wireless router in order to hack it.
To find out more information on these concepts on how hackers hack bank accounts on an ongoing basis simply join our list.
RECOMMENDED ARTICLES FOR YOU:
2. What is SSL lock and How it works
That’s all for today friends, I hope you all have liked the discussion about why hacking bank accounts is tough.
Sbi Bank Account Hacking Software Price
If you like my information or have any doubts please post your comments.